Proactive Approach
On average, for every hour of IT support you receive, there is an hour and a half of lost productivity by your employees. Whether it is a system-wide or a single user outage, downtime costs a lot of money. Our proprietary approach to preventing or quickly responding to technology failures consistently cuts downtime in half. We work with you to determine how many hours of productivity are being lost each month as well as build a corrective course of action.
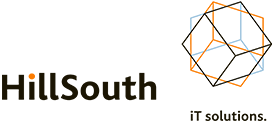
Our proactive steps include:
- Anti-virus - Configured to meet PCI compliance, our anti-virus solution prevents intrusion whenever possible, effectively quarantines existing infections, and reports back to our central server to help us stop the infection from damaging your data
- Cloud Backups - Unfortunately, data is lost even with the best prevention techniques. Our approach allows you to quickly recover, whether a file was deleted, a machine crashed, or data was corrupted
- Patch Management - We centrally test and manage Microsoft patches, closing security holes and stabilizing your system
- Periodic Maintenance - Our series of periodic maintenance steps take place in the background and keep your system running optimally without interrupting your ability to do business.
- Key Monitoring - We monitor key components of your system to identify potential hardware failures ahead of time. This allows you to replace failing hardware at a more convenient time.